Thoughts on the Aite-Novarica Group 2022 Impact Innovation Case Study
Last month, Aite-Novarica announced that Radiant Logic won their 1st Annual Cybersecurity Impact Award for Best Enterprise Security Solution for Employee and Nth Party Access. This month, they’re following up with a case study illuminating the benefits of the RadiantOne Intelligent Identity Data Platform.
This award was not one of the pay-for-play types so common these days; no, this award was vetted not only by the analyst firm but also by industry experts and several journalists. For Radiant Logic to have won this award, the panel/judging body looked beneath the surface-level of the IT security infrastructure related to implementing a Zero Trust Architecture. Especially since Radiant Logic’s solutions do not fit into standard identity management ecosystem categories but are nevertheless critically important to building a successful ZTA implementation, implementations that depend on a solid identity data foundation on which all ZTA components can rely. Avoiding custom coding and piecemeal workarounds is key to hastening and unlocking the value of identity data for this broad-reaching security architecture.
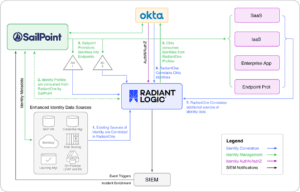
RadiantOne delivers unified identity data across the enterprise to simplify complex identity infrastructures and establish authoritative identity data for the business. Standardizing identity data access across the enterprise fulfills a critical capability often overlooked in many organizations, partly due to vendor promises that whatever IAM, IGA, PAM, or fill-in-the-blank can access the identity stores needed to accomplish their mission. It’s not that these vendors are lying; they can (eventually) get the right data to make necessary identity-related access or management decisions—it’s just at what cost.
After all, any problem in this space can be solved with enough resources. But that’s precisely the problem. According to the report,
“Internal teams working to retire technical debt were often challenged to retire identity silos due to several factors, including strong coupling to business-critical applications, lack of identity expertise on staff, limitations of underlying protocols, and lack of funding support.”
-Aite-Novarica Impact Awards, Cybersecurity
Budgets to wire identity-consuming applications to identity-providing directories and databases are constrained or don’t exist. What happens when their vendor’s underlying identity stores need to be migrated to the cloud or are obsoleted? Oh, and do the skills exist to do this kind of work and keep it updated over time? And if these resources are available, aren’t there better things they should be tasked with? Like figuring out how to build out a Zero Trust Architecture?
The primary tenant of implementing a Zero Trust Architecture is that all users, whether in or outside the organization’s network, be authenticated, authorized, and continuously validated before being granted or maintaining application and data access. The data driving these decisions must be correlated, up-to-date, timely, and derived from identity sources dispersed on-prem, legacy, and cloud technologies. Enter Radiant Logic and Aite-Novarica Group’s recognition that getting identity right the first time and every time after is what’s critically important when building out a ZTA.
The Aite-Novarica case study examined how RadiantOne was designed to support challenging and complex identity environments. They concluded that RadiantOne simplifies identity data access in enterprise-level, diverse identity ecosystems, especially environments that have grown through acquisition. RadiantOne operates in hybrid hosting models, supporting disparate identity sources. Radiant Logic solutions yield transformational value within highly regulated industries such as financial services, insurance, and healthcare, as well as many large customers in defense and federal agencies.
RadiantOne connects to all sources of user identity across the enterprise, transforming this data into global user profiles and making these profiles accessible in the exact format required by every consuming application and service. RadiantOne automates the painstaking identity tasks of aggregating, joining, correlating, and synchronizing identity data from disparate identity silos into one authoritative identity data pipeline. RadiantOne delivers a single, authoritative identity source to applications, simplifying access decisions such as authentication and fine-grained authorization even when identity data is dispersed across backend stores, all without impacting users or applications. All capabilities that are required when designing a Zero Trust Architecture.
The case study also included financial justifications for deploying RadiantOne. After all, justifying another solution to support all the solutions currently in place or planned will require some economic justification. In the case study, Aite-Novarica highlights that RadiantOne was able to deliver customer value in as little as one month with the following benefits:
- Identity transformed into business enabler: product and development processes can operate at a greater pace with one customer experiencing time-to-value being reduced from months to weeks—on every project
- Dramatic increase in project ROI: One deployment they studied saved the customer $1.4M; another customer shared that Radiant Logic delivered an integration path that enabled the integration of two merging firms, saving years of work and over $100M in IT costs
- Advanced 360-degree view of users: RadiantOne delivered clear and comprehensive views of users, providing unprecedented “identity intelligence” for operational personnel to improve onboarding and termination processes
Businesses of all types are executing strategic digital transformation initiatives. Many of these transformation projects are looking to build in Zero Trust as a critical part of their cybersecurity modernization efforts. The success of all these efforts starts with the user identity. If done well it can be an enabler—alternatively, it can be a significant impediment if done wrong
To see what your organization stands to gain from an Identity Unification approach, get in touch to discuss more.