Do you know the difference between user access reviews and access recertification? They sound like they could be interchangeable, but nothing could be further from the truth. Although both are designed to protect the resources within your information systems (IS), the user access review and the recertification of access rights are two distinct control mechanisms and do not address the same issues.
In practice, however, we tend to use the two terms interchangeably. Recent discussions with our customers have led us to believe that clarification is needed. While the differences between these two approaches may seem subtle, they are crucial. Read on to learn more about why.
The Definition and Main Aspects of User Access Reviews
The periodic user access review is one of the most widespread and unavoidable security control mechanisms for logical access rights. For example, the guidelines initiated by the Sarbanes-Oxley Act, better known as SOX, aimed to reduce fraudulent financial reporting by establishing the implementation and maintenance of internal controls that include information security protocols to ensure the security of financial information while calling for the audit of these controls to verify their effectiveness.
One aspect of all good information security protocols is periodic user access reviews. As companies continue to evolve their systems to incorporate more digital information management, it is imperative that sensitive information is only available to those authorized to view it. The purpose of an access review is to confirm that only authorized users can access secure data and revoke access from those who should not.
Data, Applications, and Infrastructure within an Organization: Who accesses what, why and how?
The periodic review of user access and entitlements is the process that allows organizations to examine which employees, both internal and external, have access to which resources within the information systems (IS) of the organization. The user access review applies to and includes all people who may have access to the organization’s information, including employees, partners and even subcontractors.
The Zero-Trust User Access Review
Because it also concerns employees and other people accessing a company’s resources off-site (via the cloud, for example), the review of user access and identities is perfectly in line with the zero-trust approach. This paradigm consists of abandoning the old practice of perimeter cybersecurity in favor of an approach that is adjusted to new processes and uses. The National Institute of Standards and Technology (NIST) defines Zero Trust as “a collection of concepts and ideas designed to minimize uncertainty in enforcing accurate, least privilege per-request access decisions in information systems and services in the face of a network viewed as compromised.” The idea is that Zero Trust goes beyond the “castle-and-moat” theory that was the basis for former methods of securing the perimeter, suggesting that trust can be considered a vulnerability with regards to security.
User Access Review and Compliance: How can you meet the challenge?
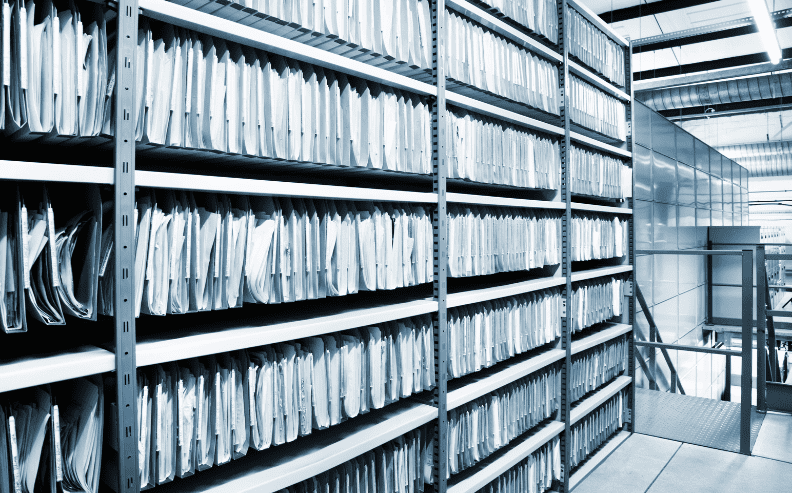
Before launching a campaign, it is important to take inventory of the user access to all resources being reviewed, ensuring that the scope accurately reflects the current situation at the time of the review by following a “bottom-up” approach. By doing this, the user access review will be more thorough and comprehensive, which also helps monitor the effectiveness of the access request process.
The Fundamentals of Access Recertification
Just like with user access reviews, access recertification is a control function using processes linked to an IGA platform. However, the challenges and purpose of the exercise differ significantly.
Recertification and the Request for User Access
Within most companies, there are more requests to grant access rights than there are requests to revoke them. Companies are continually affected by the movement of people, including new hires, departures, internal transfers of employees or service providers, promotions, reorganizations, etc. These changes have consequences related to IT authorizations and policies for users and account holders. This is where the recertification of access rights comes in, as application and business line managers are regularly asked to verify that the accesses that have been requested on behalf of their team members are still valid with regards to their current roles and responsibilities within the organization.
Tackling the Recertification of Access Rights
User access that has been previously requested and granted is periodically reviewed by department managers. The reasoning behind performing an access recertification is that, while certain access rights were requested – and approved – by a manager at one time, they may now be outdated or irrelevant and should be revoked. Regular recertification of granted user access by the resource owner or business manager can help to avoid the accumulation of illegitimate rights and the creation of potentially toxic combinations.
What are the similarities between user access review and access recertification?
Review Campaign Configuration: A Top Priority
The user access review as well as the recertification of access rights can be done manually using Excel tables. However, we highly recommend that you opt for the automation of your campaigns in order to save time and money on this practice.
Because of this, their frequency and the targeted perimeter can vary with regards to the goals and objectives of the exercise. Different strategies can be considered and implemented, including periodic, continuous, incremental and differential review practices. In order to know which one is the best for you, it is essential to pay particular attention to the configuration phase of the review project.
User access review and access recertification address different security issues. This depends on the level of sensitivity of the resources and changes within the organization as well as the audit deadlines and reports that may be imposed.
The Key Stakeholders
Business line owners and application managers have a crucial role to play. They are the only ones who have sufficient knowledge of the job functions of each member of their team, including what resources they need to access and what level of entitlement should be granted for their level of responsibility.
All these stakeholders need to review the access rights of each team member in order to ensure that the principles of least privilege and need-to-know are being respected. They must review the actual access rights as well as the incoming requests to grant access, requiring them to make the appropriate decisions by asking themselves the following questions:
• Have the access rights of each person on my team been approved?
• Are they objectionable and should they be revoked?
• Who can access what, when, why and how?
In this way, user access will be constantly monitored. Once a review campaign is completed, any identified problems, anomalies or gaps can be corrected in order to reduce the associated risk.
Notable differences between user access review and access recertification
Given the many similarities between these two control systems, it is not surprising that many confuse the review of permissions with the recertification of access rights. From the configuration to the execution of the exercise, the approach is relatively similar. However, the source data being examined is fundamentally different and impacts the scope of the project.
User Access Review: Targeting Regulatory Compliance
The periodic review of user access and permissions is based on the real and effective rights of users as recorded and reported in each system and application. This is an essential activity for anyone wishing to:
• Protect and secure the resources within a company’s information systems,
• Ensure that the security policies enforced within the organization are being respected (ISO 27001, ISO 27002, ISAE 3402, SOC 1 and 2, SOX, CMMC, HITRUST, HIPAA, CRBF, Solvency, etc.), and
• Demonstrate compliance of the company’s user access rights and respond with reports to auditors.
In fact, the periodic user access review is applied to the entire scope of accesses, regardless of their nature or the way they were obtained, either automatically or through an approved request or waiver process. In this way, the principle of completeness and accuracy, which is so important to auditors, can be met.
Recertification of Access Rights: Spotlight on the Request for Access
Access recertification primarily examines validated access requests. User access and accounts that were granted outside of the usual access request process may not be included in the scope of recertification.
Does the recertification of access rights prove compliance?
Unlike user access review, access recertification does not take into account actual rights and entitlements. It relies only on the information managed in the Identity Governance and Administration (IGA) or Identity and Access Management (IAM) system. This can cause several problems.
First, the IGA/IAM system may not manage all the accounts within the scope of the review. For example, desktop user accounts are managed in the IGA system while privileged access is managed in a PAM system. More importantly, IGA/IAM systems have only partial knowledge of the authorizations assigned to accounts. For example, macro rights (application roles or those assigned via security groups) are managed in the IGA system while fine-grained permissions are managed directly, and often manually, in the application itself. In this case, the recertification of IGA accesses will not necessarily be a true reflection of an employee’s actual rights within the application.
For this reason, the implementation of an access recertification process only using the data in IGA/IAM systems is often considered insufficient by auditors when it comes to ensuring compliance of access rights to sensitive applications and systems.
User Access Review and Recertification of Access Rights: Two Distinct but Complementary Approaches
While the protection and security of corporate resources remains a shared priority when performing a user access review or access recertification, the nature of the data and the project’s objectives differ in both cases.
One thing is certain: implementing the most effective tool is a priority for anyone wishing to gain time and efficiency in the execution of user access review campaigns which can even help to better motive and engage the team leaders and review owners in charge.
It should also be noted that it is possible to combine both the review and recertification approaches within the same process. For example, an appropriate control plan can automatically reconcile the actual rights of employees and other users in the applications with the access requests recorded in the IGA system. Any discrepancies detected can be highlighted during the periodic user access review process, alerting the reviewer to the potentially unjustified nature of an access that was not granted according to the official or standard practice within the organization.
Conclusion
To learn more about all the advantages and benefits of automating your user access review campaigns, please contact us. Together, we can take the next step towards effortless user access compliance within your entire organization.