As I prepare for Gartner IAM UK later this month, I find myself confronting an uncomfortable truth that many security leaders are reluctant to acknowledge: The massive investments organizations are making in identity security tools are paradoxically creating more vulnerabilities than they solve. After years in the Identity market advising Fortune 500 CISOs, I’ve observed that the relentless pursuit of new detection capabilities has created a dangerous industry blind spot – one that sophisticated attackers exploit with ruthless efficiency.
The Paradoxical Security Arms Race We’re Losing
You’ve likely experienced it firsthand: the executive board meeting where everyone nods in agreement as you showcase your latest identity threat detection investments. New alerts, new dashboards, new “AI-powered” capabilities that promise to spot the needle in the haystack. The board feels protected. Your team feels empowered.
Yet breaches continue at an alarming rate.
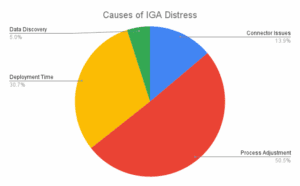
Identity security fundamentally has a data problem. The industry lacks standards on data models and identity data silos exist across fragmented, disconnected systems. Even modern IAM solutions lack the ability to normalize and correlate identity data across a hybrid enterprise. This fragmentation weakens security posture resulting in greater vulnerability to identity-based threats.
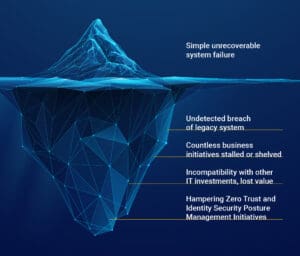
The paradox is painfully simple but rarely discussed: by focusing obsessively on detection while neglecting the integrity of the underlying identity data itself, organizations have built sophisticated security castles on foundations of sand. Every specialized security tool added to the enterprise ecosystem creates its own silo of identity data—each with a partial view of the identity landscape but none with complete visibility. As these tools proliferate, they create a false sense of coverage while critical identity risks fall through the cracks between systems. The irony is striking: the very tools meant to improve visibility often obscure the complete picture.
The Hidden Attack Vector Your Tools Can’t See
The most dangerous aspect of this paradox is what I call the “identity visibility gap” – the dangerous blind spot created when organizations lack a comprehensive, accurate view of their identity ecosystem.
This gap exists not because organizations don’t care about security, but because traditional approaches to identity management weren’t designed for today’s complex, distributed environments.
Today’s threat actors know they no longer need to defeat your detection systems directly. Instead, they exploit the seams and inconsistencies in your identity data itself – the places where different systems have conflicting information about the same identity. These inconsistencies create shadow zones where attackers can hide in plain sight.
This identity visibility gap becomes exponentially more dangerous when we consider the explosive growth of machine identities. These non-human identities—service accounts, API keys, application credentials, and cloud workloads—are multiplying at 3-5 times the rate of human identities due to automation, DevOps practices, and increasingly, GenAI implementations.
Unlike human identities, machine identities rarely “leave” the organization. Instead, they grow over time, often with privileges that far exceed their essential operational requirements. The most concerning pattern? These machine identities form complex, undocumented webs of interconnection. A compromised low-privilege service account in one system can often provide lateral movement paths to critical systems through inherited or transitive trust relationships no human administrator fully understands. These “ghost roads” through your infrastructure represent the attack paths of choice for sophisticated threat actors.
The Uncomfortable Math of Identity Security Investment
The math is uncomfortable but undeniable. Gartner’s 2024 report highlights that poor identity hygiene is the primary enabler of identity-based attacks, as attackers exploit inconsistencies and gaps in identity data. Despite this, organizations allocate approximately 80% of their budgets to detection and response tools, leaving less than 20% for prevention and hygiene measures.
I would argue that even today’s approach to AI in identity security falls woefully short. Most “AI-powered” identity security tools simply flag statistical anomalies: “This user accessed System X at an unusual time.” This surface-level detection is the equivalent of a home security system that can tell you a window is open but can’t determine if it was forced.
This 80/20 detection-prevention imbalance creates a vicious cycle: poor identity data quality leads to excessive false positives in detection systems, which drives investment in more sophisticated detection tools, which then generate more alerts based on the same poor-quality data. Meanwhile, the underlying vulnerability – fragmented, inconsistent, and often outdated identity data – remains unaddressed.
A Combined Arms Approach: A Radical Rethinking
In military operations, a “combined arms” doctrine is a strategy that recognizes that different capabilities, like infantry, armor, artillery, engineers, and aviation, must work in concert to achieve victory. This approach recognizes that no single arm or capability can decisively defeat a determined enemy on its own, especially in complex and dynamic battlefields. Identity security is no different. It requires balancing and integrating complementary capabilities rather than relying heavily on any single approach.
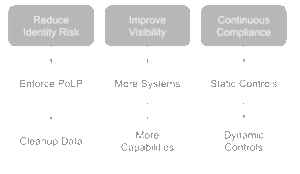
We need a combined arms framework that fundamentally rebalances identity security around two equal forces: Identity Security Posture Management (ISPM) for prevention and Identity Threat Detection and Response (ITDR) for detection.
ISPM functions as your defense, proactively assessing and strengthening your identity infrastructure to catch vulnerabilities before attackers exploit them. ITDR operates as your offense, hunting down threats in real-time and responding swiftly when identities are compromised or misused.
The critical insight is that these capabilities must operate from a foundation of high-quality, unified identity data to be effective. When identity data lacks completeness, accuracy, and timeliness, even the most sophisticated security tools become compromised in their effectiveness. This fragmentation creates dangerous blind spots that sophisticated attackers eagerly exploit.
Data-Centricity: The Missing Foundation
The core challenge isn’t a lack of security tools—it’s a data problem. Most organizations suffer from fragmented, inconsistent, and often outdated identity data scattered across numerous repositories. Weak identity posture creates major gaps through over-permissioned accounts that unnecessarily expand the attack surface, orphaned accounts that maintain lingering access long after users leave, and identity sprawl with unmonitored identities scattered across cloud, SaaS, and internal systems.
As Gartner noted in their 2024 report on identity hygiene, good data is key in limiting the identity attack surface. In practice, this means organizations must ensure identity records (accounts, credentials, entitlements) are accurate and up-to-date to shrink potential breach points. Without this foundation, security tools operate with incomplete information, significantly reducing their effectiveness.
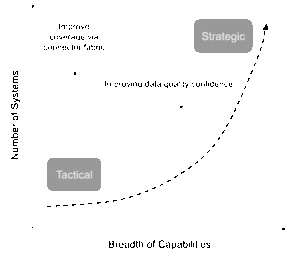
What does a data-centric approach to identity security actually look like in practice? It begins with three core capabilities that together form the foundation of truly effective identity security:
1) Real-Time Identity Data Lakes: Visibility Before Action
True identity security begins with consolidated visibility – not just periodic snapshots, but a real-time, complete view of your entire identity ecosystem. This approach differs radically from traditional perimeter-focused security by creating a unified identity intelligence layer that spans all identity repositories.
A global healthcare provider implemented this approach and discovered previously unknown machine identities with excessive privileges across their environment. These machine identities had been created by various operational teams over years without centralized oversight or governance. The most alarming discovery? Their existing security tools had completely missed these identities because they were looking for suspicious behavior, not missing or incomplete identity data.
2) AI-Powered Identity Analytics: Finding Patterns Humans Miss
The second critical component involves leveraging artificial intelligence to transform raw identity data into actionable security intelligence. While everyone talks about AI in security, few are applying it to the most fundamental element: understanding the relationships and patterns within identity data itself.
Sensemaking of complex data relationships is a key strength of GenAI, a topic I discussed during last year’s Identiverse Keynote. However, all AI capabilities are limited to the breadth and quality of the data they can see. Incomplete or worse, inaccurate data will lead to misinterpretation by even the most advanced AI capabilities. When provided with comprehensive and accurate identity data, AI analytics can identify subtle but significant patterns such as excessive privilege accumulation which would otherwise remain undetected for years. Patterns like these will not be obvious in any single system but become apparent when analyzing the comprehensive identity data lake.
Effective AI for identity security must go beyond anomaly hunting to relationship mapping. This means:
- Semantic understanding: Rather than treating “Admin” roles across systems as unrelated entities, advanced AI can understand their equivalence despite different naming conventions.
- Temporal analysis: Identifying permissions that have drifted over time, creating toxic accumulations of access that would never be granted at once but accrue gradually.
- Risk correlation: Connecting identity attributes with vulnerability data to identify which excessive permissions create actual attack paths versus theoretical risks.
By addressing the systemic data visibility issue, organizations significantly improve their security posture and reduce the attack surface.
3) Continuous Resilience: Beyond Detection to Adaptation
The final capability involves building continuous resilience through proactive identity security practices that adapt to emerging threats. Instead of point-in-time assessments, this approach implements continuous monitoring and automatic remediation processes.
A global retailer implemented our continuous resilience framework and reduced their response time to identity-related security incidents from days to minutes. When a potential compromise was detected, their security team had immediate access to complete identity context – seeing all the user’s accounts, entitlements, access patterns, and risk factors across every system – rather than manually gathering this information from multiple sources during an active security incident.
The Future of Identity Security: My Controversial Prediction
Looking ahead to 2027, I’m making a prediction that may seem controversial: the identity security industry will experience a major market correction as organizations realize that their massive investments in detection tools built on poor-quality identity data have created more risk than they’ve mitigated.
In “Predicts 2024: IAM and Data Security Combine to Solve Long-Standing Challenges” Gartner suggests that by 2026, “organizations adopting top data practices within their IAM program will realize 40% improvement in time-to-value delivery for IAM and data security program objectives”. I believe this understates the impact. Organizations that balance prevention and detection on a foundation of high-quality identity data will see not just incremental improvements but transformative change in their security posture.
We’ll Witness Several Major Shifts:
- First, identity data will be recognized as critical infrastructure, deserving the same level of investment and protection as traditional security components. Forward-thinking organizations are already building dedicated identity data operations teams that cross the traditional boundaries between security, IT, and compliance.
- Second, AI will revolutionize how we manage identity security, but not in the way most vendors currently claim. Rather than simply detecting anomalies faster, truly advanced AI will help organizations understand and manage the quality, completeness, and relationships within their identity data itself.
- Finally, we’ll see a convergence of identity and data security platforms, as Gartner predicts that “by 2027, 70% of organizations will combine data loss prevention and insider risk management disciplines with IAM context to identify suspicious behavior more effectively.” This convergence will eliminate the artificial boundaries between these domains that attackers have exploited for years.
Breaking the Paradox: The Path Forward
The path to breaking this identity security paradox requires a fundamental shift in thinking. Instead of treating identity data as a byproduct of security processes, we must recognize it as the foundation of effective security itself.
By adopting a data-centric approach to identity security – one that emphasizes the quality, completeness, and timeliness of identity data – organizations can significantly reduce their attack surface and strengthen their overall security posture. In an era where identity has become the primary security battleground, this approach represents the most effective strategy for defending against increasingly sophisticated threats.
As you assess your own identity security investments, I urge you to ask yourself: Are you perpetuating the identity security paradox by pouring more resources into detection while ignoring the data quality issues that undermine your entire security architecture?
In my next blog, “Breaking the Identity Security Paradox: Building a Data-First Architecture,” I’ll share specific implementation strategies for organizations looking to rebalance their identity security approach, including detailed case studies from global enterprises that have successfully made this transition. I’ll also explore how the coming wave of AI in identity security will fundamentally change how we think about protection, detection, and response.