Best Practices for AI Powered IVIP
AI seems to be on track for taking over the world in the coming years. Whether the hype is to be believed and we will all be replaced by AI-powered cyborgs in 10 years, it is fair to say that AI has created huge opportunities for both security and productivity improvements across a range of sectors, public and private and for entities of all sizes.
Two key questions emerge: how will AI impact identity and access management and how can identity and access management adapt to protect what is in essence a brand new technology type?
AI in IAM and IAM for AI
Let us tackle these questions from the lens of IVIP. But first, what is IVIP and what does it entail? “Identity Visibility and Intelligence Platforms” was a term coined by Gartner in 2025 to address some of the key challenges facing identity governance and administration programmes and some privileged access management deployments. Namely a lack of real-time visibility, a difficulty in handling more dynamic environments and the “speed of cloud” as well as a general lack of threat detection capabilities at both the data and post-authentication activity level.
IVIP aims to provide this overlay component and support a range of end to end use cases that leverages existing technology investments but delivers a more security-focused approach. This security aspect is a real evolutionary step with respect to IAM. The past two-decades have seen a range of security evolutions for networks, data end points – with network security and data security emerging into multi-billion sectors. As our IAM infrastructure is now used to empower productivity, zero trust, security and user experience, it has by design become an attack vector. To that end being able to support security-related constructs like discovery, visibility and anomaly detection now become critical. IVIP aims to support that.
Other terms that have become synonymous with security for IAM include ISPM – identity security posture management and identity threat detection and response (ITDR). The former is often focused upon the identity data layer (namely profiles, permissions and policies) with ITDR aimed at detecting post-authentication anomalies including malicious access control usage and application activity.
It is becoming increasingly clear that the typical pillars of IAM capabilities (such as IGA, PAM, IDP and strong authentication) are no longer enough to improve security nor productivity. They are no longer enough to prevent even the most basic credential-privilege escalation-lateral movement attack flows due to a lack of visibility and poor hygiene maturity.
So if we tackle the two overlay identity security capabilities focused on end to end data management and runtime activity, what can AI do to help accelerate improvements?
It is important to identify where the pain points and risk “heat” may exist and where existing non-AI approaches to improving data hygiene and runtime detection are sub-optimal.
A secondary aspect to consider, is how existing IAM concepts and components can be used to protect the emerging use of AI. Not all AI is the same and there are many nuanced aspects that should rely heavily on strongly functional verification, attestation, authentication and authorization services. If we treat agentic-AI like a digital employee and not just an abstract software related component, we can start to realign our risk and threat models more accurately.
The agentic world generates multiple questions around delegation of permissions, in-personation use cases and just in time access and how that should relate to the permissions and context of the associated carbon-life form.
For example, an AI agent via the model context protocol (MCP) will have access to a vast and sprawling underlying data set.
Should the agent simply assume the permissions of the human “using” the agent? How is the cascading access and risk determined and analysed?
Will the access need to change – and if so is that a legitimate expectation to complete an objective? Agents will be assigned objectives and not just specific well defined tasks – so it may well be a legitimate requirement for the access permissions to alter and grow as the agent learns, optimizes and understands the objective it has been set in more detail – just the same as a human snowballs more responsibility within a project, needs access to more systems with more authority. Their permissions grow too. How can an access request model, authorization policy and enforcement framework cater to this?
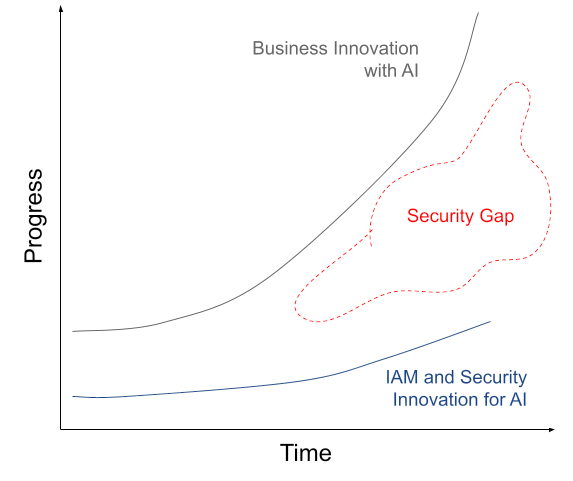
Today, there is a gap in the innovation maturity and adoption of AI and what the existing identity and security architectures and controls can support. Perhaps only by the addition of AI capabilities into the identity and security landscape can the gap be narrowed.
Identity Data Opportunities
Identity and Account Discovery, Correlation and Management
If we look at the identity data layer – the typical profiles, permissions and policies focus – what can be identified as firstly being of high impact to security and productivity, but is also operating sub-optimally?
An immediate concern is that we can only protect what we know about. This clearly extends to many IAM projects due to a limited view and management control of all identities that exist within the organisation. It is quite common to deploy identity governance and administration (IGA) or privilege access management (PAM) tools to a small number of applications. Perhaps only those under the scope of regulation, but more likely due to connectivity and integration challenges. Of the systems under management, an ability to discover all identities and accounts within that system is not always possible.
Secondarily an inability to link accounts to other accounts in different systems and in turn link to an anchor identity is essential for context and analysis, but also to fulfill provisioning and de-provisioning change events.
Guidance: Correlation and recommended correlation can become a simple and highly automated process in the AI-led world. The result is an instantly more connected and broad visibility of the identity assets play.
Account and Permissions Ownership
Ownership of discovered assets is rarely optimized. Identifying who should own a service account or non-human identity is increasingly avoided due to the numbers involved and the highly dynamic nature of these types of identities. Being able to identify accountable and responsible owners and integrating with chatops infrastructure (think Slack and Microsoft teams) in order to notify, engage and assign accounts improves access request and approval functions and also improves the ability to identify changes to a secure running state of identity data.
An extension to this use case, is that of being able to effectively massage permissions. From directory groups, application-specific access control entries, roles and higher level policies – a lack of ownership instantly results in a lack of accurate posture, reporting and accountability.
Guidance: The analysis of permissions events and meta data (who created, requested changes, which departments the accounts associated with the permission reside in and so on) is a clear machine learning and AI-lead initiative that can quickly be used to recommend and contact owners.
Access Request and Review Effectiveness
Whilst those two use cases are often overlooked, two use cases that are constantly in flight in many organizations are the access request and access review processes. Access requests occur daily and are part and parcel of all organisations, even those who have no regulatory obligations. Working out which system and in turn which permissions to request access for can be difficult for non-technical users. The fix is to “copy” access from a colleague who acts as a model user. The result? Access proliferation and the constant “copy and pasting” of poor access control logic. An improvement is to use AI-generated context – likely in the form of co-pilot and assistance technology. This can be based on natural language processing (NLP) and non-technical queries and answers based on the business tasks and functions the end user wishes to complete.
Guidance: By analyzing existing users, risk and zero stranding privileges assistance technologies such as chatbots can navigate access requests in a way that automatically approves and assigns based on context such as work environment, ITSM tickets and risk.
Access reviews are constantly being optimized. As numerous compliance initiatives require this periodic process to be completed securely and effectively it is not a use case that is going to become obsolete anytime soon – yet with continued optimization and automation, perhaps many aspects of it can be removed from the human’s workload.
Guidance: A clear optimization opportunity is to identify and in auto-remove the difference between the permissions associated with a user (even after successful access request and approval) and the permissions the user under review is actually using. This is a pragmatic approach to quickly reduce the identity attack surface, but also streamline birth-right permissions associated with particular business roles and job functions.
Identity Security Opportunities
Anomaly Discovery
We should also consider the identity landscape from a more security-orientated perspective. This often brings into consideration anomaly discovery. Whilst this could be behaviour and post-authentication based, we must also consider anomalies within the aforementioned data layer too. So misalignment in existing identity data patterns (account to permissions associations, access request history and context, access usage) as well changes to configuration.
Anomaly analysis will require an ability to discover and in turn create baselines of “standard” and expected change. This could be through observation of existing and historical data sets. Who requested access to that, when, and how it was approved. Of correctly assigned permissions, which were being used? Under what circumstances were they used? Time of day, origin device and location and what happened before and after the permissions usage? This level of “observability” can often take time to create, but provides a higher-fidelity of decision making with respect to identifying something of suspicion, when to respond to how to respond.
Guidance: Machine learning against existing access request and usage patterns can provide a solid foundation for baselining standard patterns of usage and ways to identify suspicious changes to the secure running state of the identity data plane.
Misconfiguration Identification
The IAM landscape is complex. Multiple systems, identity types and access control logic points are needed to drive productivity and security success. All of which are growing in both volume and breadth of deployment. Cloud service provider (CSP) IAM components for example require specialist personnel and tools to administer features like federation, credentials, roles and permissions for humans and workloads.
Mistakes and misalignment to controls and compliance requirements are common. The “scanning” of IAM configuration is not a new concept but can become increasingly difficult to automate due to the constant change in the surrounding business and cyber threat landscape. Changes to IAM policy and configuration can also have significant user impact if the wrong choices are made – so the simulation and A/B testing of identity configuration changes is often asked for – but that too can be difficult to sustain.
Guidance: The comparison of existing secure running states of IAM configuration need to be compared not only to “best practice” and regulatory requirements, but also to changes to business needs and external cyber threat intelligence. Identification of remediation actions is only one aspect, and the ability to perform updates to multiple types of identity configurations seems a likely candidate for agentic-AI with some level of human in the loop approval.
Risk Response
All of the previously mentioned options are grounded in an ability to identify risk, assess it appropriately and apply the appropriate response. The modern enterprise is not short of data and using that data to alter the IAM landscape more dynamically is key to both driving value from the underlying IAM components, but also improving their security posture.
IAM risk response should no longer just focus upon changes to permissions – which historically could take days to complete via poor provisioning and connector frameworks. Today risk can be identified at any part of the identity lifecycle – especially so post-authentication and during session usage. An ability to identify risk (which requires more security signals) and an ability to do something actively once that risk is deemed above a certain threshold is critical to modern identity security. Concepts like the shared signals framework (SSF) and continuous access evaluation profile (CAEP) are strong indicators of the industry both acknowledging this and moving forward with agnostic solutions.
Guidance: Leveraging a more connected identity security fabric that includes a broader array of security signals is a foundational requirement. An ability to respond via a coordinated and broad approval and remediation model will result in a more fine-grained and rapid approach to threat recovery.
About The Author
Simon Moffatt has nearly 25 years experience in IAM, cyber and identity security. He is founder of The Cyber Hut – a specialist research and advisory firm based out of the UK. He is author of CIAM Design Fundamentals and IAM at 2035: A Future Guide to Identity Security. He is a Fellow of the Chartered Institute of Information Security, a regular keynote speaker and a strategic advisor to entities in the public and private sectors.