The State of Identity Security: Why Identity Is the #1 Cyber-Attack Vector
Consistently, researchers point to identity as the number one cyber-attack vector. It provides the path of least resistance that fuels ransomware attacks, data breaches, and other incidents that can be detrimental. However, this isn’t a new problem for Chief Information Security Officers (CISOs): In 2024, 90% of organizations experienced at least one identity-related incident.
Cybersecurity teams are in a race with the bad guys to minimize the identity attack surface before it can be exploited. For security leaders to earn a spot on the podium, and ensure attackers finish dead-last, they need to first look back, rather than forward, to understand how the state of identity security came to be.
In this blog post, we lean on the insights shared in Radiant Logic’s new podcast, Radio Logic. Episode 1: The State of Identity Security pieces together why identity has become the favored attack vector, as well as what security leaders can do to outsmart adversaries.
Why Identity Wasn’t Built for Cybersecurity
As Simon Moffatt, founder and CEO of analyst firm The Cyber Hut made clear to Radiant Logic Sr. Vice President Anders Askasen in the first episode of Radio Logic:
“Identity was about productivity and compliance… it wasn’t really built for security.” — Simon Moffatt
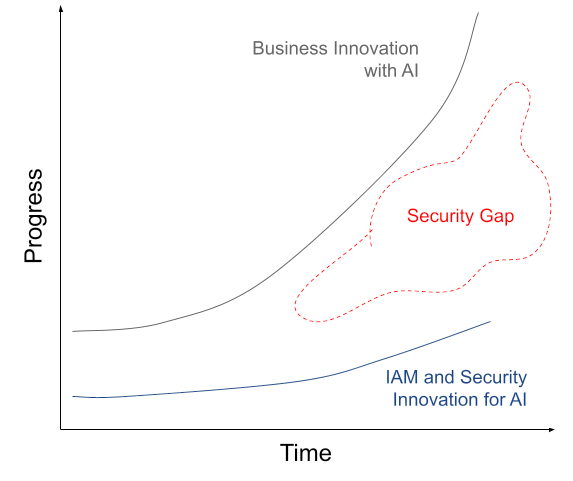
To tackle identity security in 2026, leaders need to look back at the ways in which identity and access management (IAM) and identity governance and administration (IGA) grew separately, rather than with cybersecurity. Moffatt and Askasen agreed in their conversation that enterprise identity efforts were originally tied to operational business needs, rather than potential security risk.
Identity is still integral to business efficiency in 2026 and should be treated as such, Moffatt stressed. However, this context of how enterprise identity has historically been prioritized identifies a gap in cybersecurity strategy – making the identity attack surface of today more understandable.
The Expanding Identity Attack Surface in Modern Enterprises
On top of this lack of security prioritization for identity, digital transformations such as on-premises solutions to the cloud and software-as-a-service (SaaS) products have created fragmentation within enterprises. This hybrid collection of different technology architectures makes it even more difficult for enterprises to understand their identity ecosystem.
“It’s been a gradual occurrence, but equally it’s a sort of perfect storm of legacy technology, isolated and siloed security components. Plus, we have more identities to manage.” — Simon Moffatt
Because there is no cybersecurity technology today that doesn’t rely on identity, as Moffatt put it, security leaders need to find a unifying control that can account for this fragmentation. This control, also known as an identity layer, can help to bridge the gap between IAM/IGA and cybersecurity.
“You need that identity layer under control… bringing all these different legacy silos and SaaS applications under one roof.” — Simon Moffatt
Once that unifying identity layer is in place, cybersecurity teams will have a starting point to begin reducing their organization’s identity attack surface. This identity visibility will provide defenders with a comprehensive picture of the multitude of identities that exist within enterprises – making it easier to strive for a Zero Trust ecosystem. As Askasen noted: “If you can’t see it, you can’t manage it.”
The Three Identity Problem
Having visibility into the identity ecosystem does come with a key challenge: Enterprise identities are no longer solely human. Moffatt stressed that despite modern enterprises still not having a confident grip on the security of human identities, continued digital transformations have brought new identities that need managing to the CISO’s desk.
For example, non-human identities (NHIs), which often outnumber humans 10-to-1, and come in the form of service accounts, APIs, workloads, and machines are poorly governed due to unclear ownership and minimal monitoring. Moffatt stressed that “we’ve not solved this NHI problem,” which only increases the identity attack surface.
There is also identity’s newest frontier: Agentic AI. These identities exist as autonomous agents that analyze, decide and act on key processes within the enterprise, creating a new threat landscape that attackers can exploit. Moffatt characterized the risks that stem from Agentic AI identities as adding children to a workforce: “it’s a bit like giving permissions and control to a toddler.”
As a result of these digital transformations, the state of identity security is now defined by the Three Identity Problem: Enterprises must secure human, non-human and Agentic AI identities before attackers can exploit them.
Context Matters
Every CISO strives for their organization to maintain a Zero Trust architecture, so that they can protect their organization from both internal and external threats. Identity security, which historically has been left outside of cybersecurity conversations, now demands that Zero Trust must be applied to human, non-human and Agentic AI identities. As Moffatt put it in this episode of Radio Logic, gaining context of these identities is where cybersecurity teams should start.
“Zero Trust is all about context, and the more information you have, the better decision‑making you can achieve.” — Simon Moffatt
For deeper insights into the consequences of legacy identity technologies, the threats plaguing identity security today, and how CISOs can best move forward to minimize the identity attack surface, watch or listen to Radio Logic Episode 1: The State of Identity Security.